Executive Summary
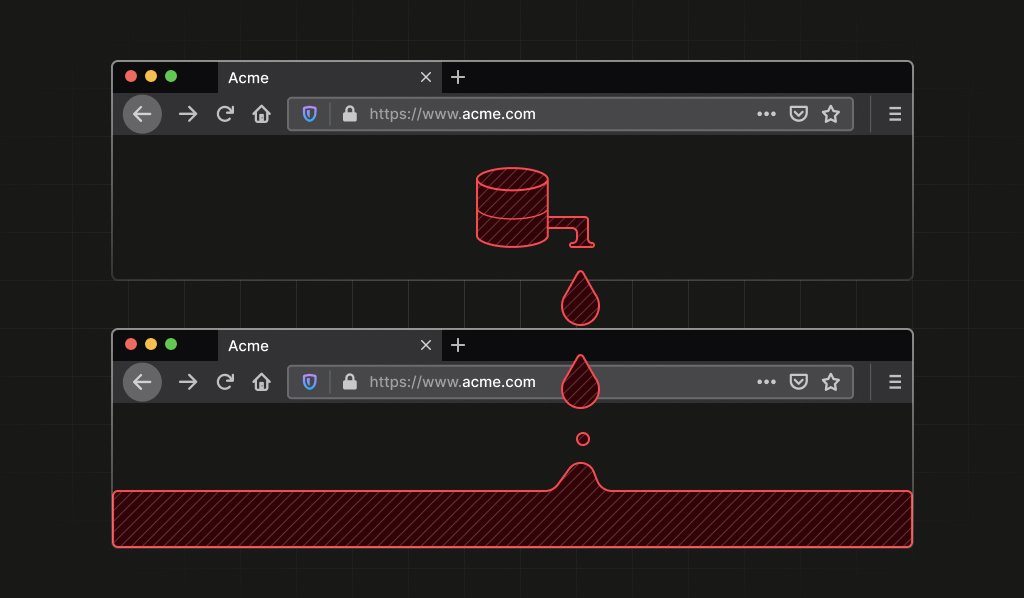
- Researchers discovered a stable Firefox identifier linking private Tor identities.
- This vulnerability compromises user anonymity and can be used for fingerprinting.
- Users can mitigate this issue by exiting Tor Browser at the end of each session.
The Buzz Score
The Internet’s Verdict: 70% Hyped, 30% Skeptical
Forum Reactions
Many users are concerned about the implications of this vulnerability. As one user noted:
why would this company report this vulnerability to Mozilla if their product is fingerprinting? Isn’t it better for the business (albeit unethical) to keep the vulnerability private, to differentiate from the competitors?
Others emphasized the importance of proper browser hygiene:
Make sure to exit Tor Browser at the end of a session. Make sure not to mix two uses in one session.
Technical Implications
The identifier can persist as long as the Firefox process remains running, highlighting the need for users to be mindful of their browsing habits.
Focus Keyword: Tor Browser
Leave a Reply