Executive TL;DR:
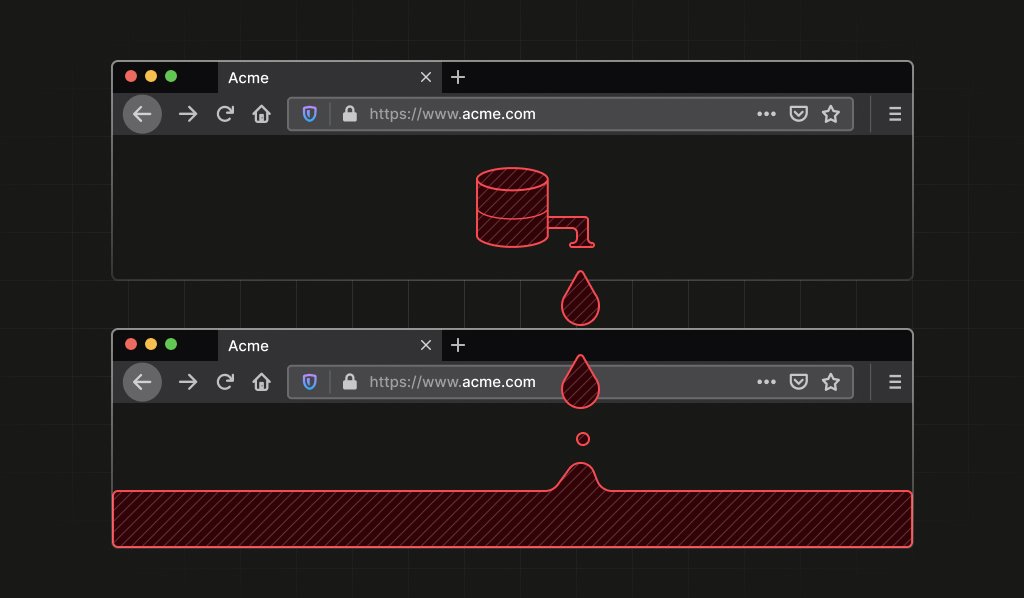
- Researchers discovered a Firefox identifier that can link private Tor identities.
- This vulnerability compromises user anonymity and can persist across sessions.
- Users are advised to exit Tor Browser at the end of each session to mitigate the risk.
The Buzz Score
The Internet’s Verdict: 70% Hyped, 30% Skeptical
Forum Reactions
Users are concerned about the implications of this vulnerability, with some questioning the decision to disclose it to Mozilla.
Very cool research and wonderfully written. I was expecting an ad for their product somewhere towards the end, but it wasn’t there! I do wonder though: why would this company report this vulnerability to Mozilla if their product is fingerprinting?
Others are critical of the architecture that led to this vulnerability, suggesting alternative solutions.
Why is this global keyed only by the database name string in the first place? The post mentions a generated UUID, why not use that instead, and have a per-origin mapping of database names to UUID somewhere?
Mitigating the Risk
Users can take steps to protect themselves, such as exiting Tor Browser at the end of each session and avoiding mixing different uses in one session.
Make sure to exit Tor Browser at the end of a session. Make sure not to mix two uses in one session.
Focus Keyword: Tor Browser
Leave a Reply